
Endpoint Protector
DLP for Enterprise and Small-Medium businesses.
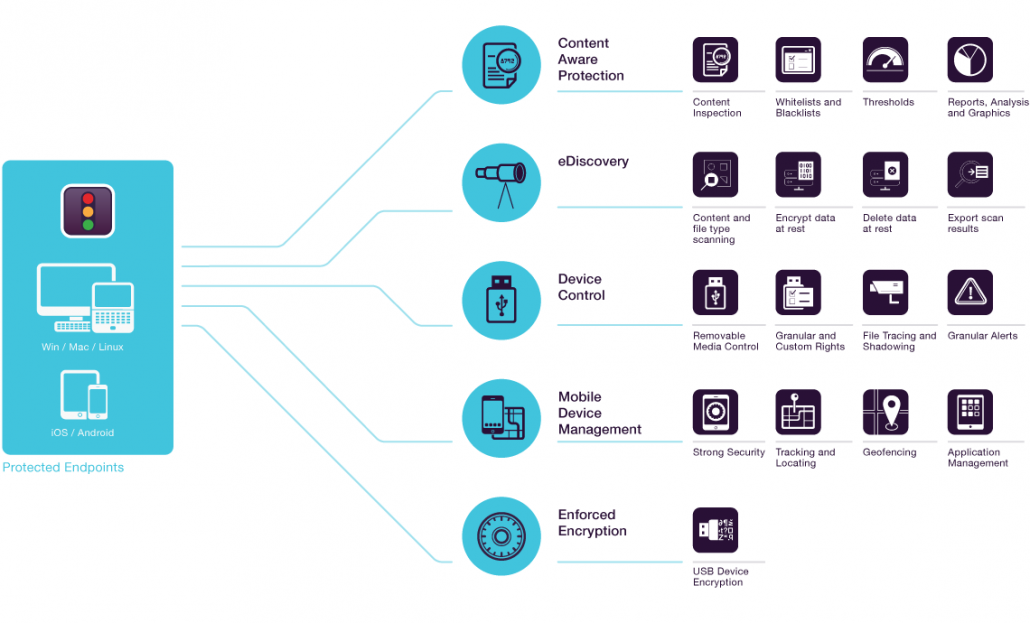
Endpoint Protector is an easy to use, cross-platform Data Loss Prevention tools that ensure seamless control of USB and peripheral ports, scan data in motion and data at rest, enforce encryption and offer enterprise mobility management. Up and running in 30 minutes. Common Criteria EAL2 Certified. Unbeatable value.
CoSoSys Recognized for its Endpoint Protector Solutions in the February 2017 Gartner Magic Quadrant for Enterprise Data Loss Prevention. Read more
Endpoint Protector Overview
Watch the Video
CoSoSys Endpoint Protector offers a rich portfolio of security products and features for network device control, endpoint security and data loss prevention (DLP) for Windows and Mac OS X, as well as the development of applications for portable storage device encryption and enhancement.
Protect your network and sensitive data from threats posed by portable storage devices, cloud services and mobile devices.
Portable storage devices such as USB flash drives, smartphones, tablets and cloud services like Dropbox, Google Drive may cause severe issues when it comes to controlling data use within and outside the company. As a full Data Loss Prevention (DLP) product available for Windows and macOS, Endpoint Protector 5 prevents users from taking unauthorised data outside the company or bringing potential harmful files on storage devices.
The Content-Aware Data Loss Prevention, eDiscovery, and Device Control modules are available for Windows, macOS, and Linux.
Enforced Encryption
For USB Devices, Windows and macOS
Allows for IT Administrators to extend their Device Control policy and make sure all confidential data transferred to USB storage devices is automatically encrypted. Via a secured password, users can safely transfer confidential data and access it on any computers or only on authorized ones.
Device Control
For Windows, macOS, and Linux
Having the possibility to control USB devices and peripheral ports activity for employees’ computers from a simple web interface simplifies IT Admin’s jobs. Strong device use policies ensures proactive protection for a safer work environment with removable storage devices.
Content Aware Protection
For Windows, macOS, and Linux
Detailed control over sensitive data leaving computers and endpoints in the network. Through content inspection, transfers of important company documents can be logged and reported. Based on your company policy, file transfers can be allowed or blocked.
eDiscovery
For Windows, macOS, and Linux
Endpoint Protector eDiscovery scans sensitive data stored on endpoints. It offers the ability to setup scans based on specific file types, predefined or custom content, file name, Regular Expressions or HIPAA protected content. Based on scan results, remediation actions like encrypting and deleting data for data breach protection can be carried out.
How Endpoint Protector Works?
Endpoint Protector Datasheet
Cososys’ flagship product provides all the features needed to secure sensitive data from threats posed by portable storage devices, cloud based services and mobile devices.
Download Endpoint Protector Trial
Available as a Virtual Appliance, you can quickly and easily trial the effectiveness of Cososys’ data loss prevention solution. Request your trial today.
