The MetaAccess Platform
The complexities involved in visibility and control over what devices are accessing your network and are those devices secure continue to grow, even more so with the increasing work from home scenario. Adding to the complexity is the myriad point products generally needed to gain this visibility and control. MetaAccess is one solution giving your organization secure network access and deep endpoint compliance. With this one platform approach, you can greatly simplify ongoing management, reducing time, effort and most importantly, risk.
Secure Access
Remote Work Requires Greater Security
Common cybersecurity issues include Advanced Persistent Threats and Distributed Denial of Service (DDoS) attacks. Remote workers are particularly vulnerable to these attacks, and we need a more effective solution than the VPN of old. Software Defined Perimeter (SDP) increases security without increased cost or throughput degradation compared to VPN solutions, with a better overall user experience.
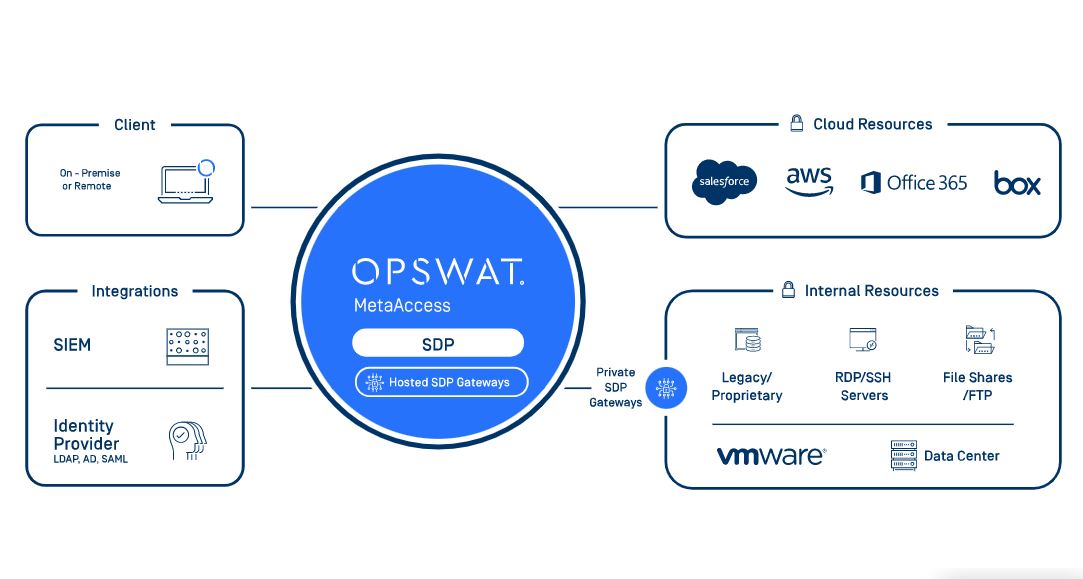
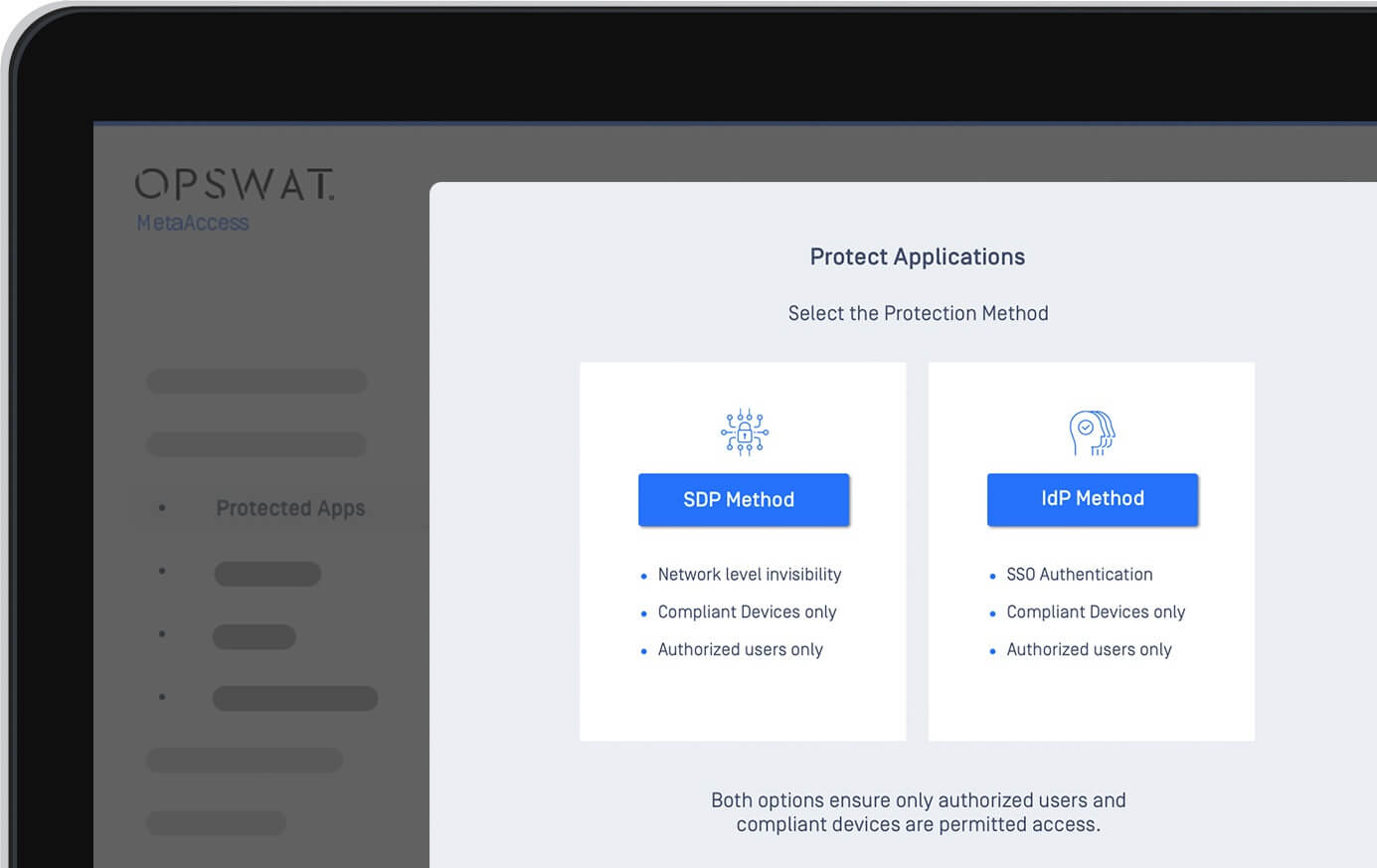
Access to Cloud Applications.
If access is to a cloud application, additional security risks can be incurred. An alternative method for security to cloud applications is also included in the MetaAccess Platform with Cloud application Protection via SAML integration (i.e. Okta, Ping Identity, Other Identity Providers (IdP) support).
MetaAccess addresses the complex BYOD ownership problem by providing the user’s identity (IdP or application user name) for each device, when accessing cloud applications. This dramatically increases unmanaged device control, without requiring any IT infrastructure changes, network traffic manipulation, or mobile device management (MDM).
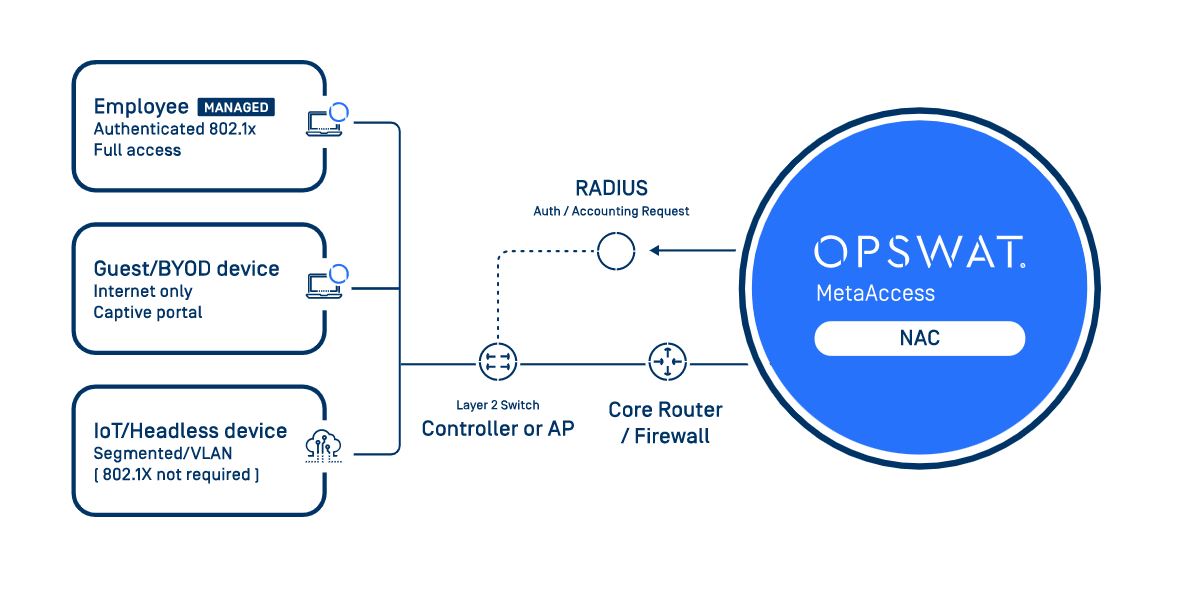
Secure Access On-Prem
It will always be important to ensure secure access and control for on-prem devices. It can be difficult to even know all the devices that are on your network, and to block any unauthorized or non-compliant access. MetaAccess Network Access Control (NAC) gives you this visibility, blocking any unauthorized device, as well as ability to audit, warn or quarantine any device that is non-compliant with your policies. MetaAccess is available with both agent and agentless solutions, and can integrate with many 3rd parties to automate threat prevention, enable enhanced reporting and more granular policies.
Single Platform & Flexibility
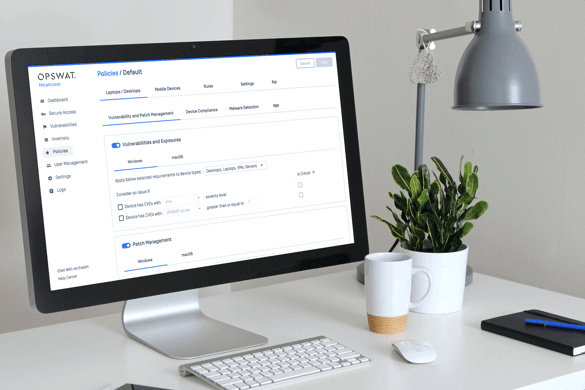
One Management View
MetaAccess dashboard management provides the visibility and management tools needed from one interface. See in total how many devices have accessed the network, whether the access method is with SDP or classic SAML/IdP integration. Know how many devices are compliant or not and drill down to specific devices to understand the issue. If executive access is needed right away, select the device and Allow Access.

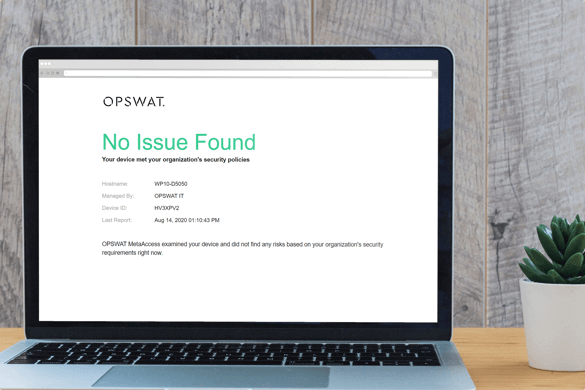
Positive End User Experience
It is extremely easy for a user to self-remediate, while at the same time educating the end-user on the importance of the non-compliant issue. A customizable page will be displayed sharing WHAT is the issue, WHY it’s important, and HOW to resolve in a step-by-step manner. With SDP, an end-user will log into their application with SSO the way they always have, whether remote or on-prem, making it easy and comfortable.
IT Flexibility & Ease of Management
MetaAccess configuration options gives flexibility to ascertain which issues should require blocked access versus notification, and to set personalized thresholds. With each function in our advanced endpoint compliance, the configuration can be setup to match your organization’s policies.
MetaAccess is available with an easy registration and deployable in a matter of hours or days. There is extensive documentation and training, and no third party services are required. The OPSWAT goal is to unify and simplify the overall experience both for IT and the End User.