MetaDefender
Advanced Threat Prevention Platform
MetaDefender is a cyber security platform for preventing and detecting cyber security threats on multiple data channels.
Advanced Malware Threat Prevention
MetaDefender protects organizations from cybersecurity threats in data that originates from a variety of sources, such as web, email, portable media devices, and endpoints. The MetaDefender philosophy is:
- Any file could be infected
- Any file could be attempting to exploit a vulnerability to compromise a network
- Single anti-malware engines, next-gen firewalls, sandboxes, machine learning, IPSes, and proxy anti-malware solutions do not provide adequate cybersecurity protection on their own
Organizations have difficulty tracking and securing all data transfer channels that expose them to security threats, especially large enterprises with thousands of employees and contractors. Data transfer channels, such as file uploads, portable media devices, and email attachments, all have the potential to carry targeted attacks that can damage an organization’s reputation, financial standing, customer relationships, and for critical infrastructure, sensitive equipment and the facility itself.
Highlights
Prevent Zero-Day Attacks and Evasive Malware
Most cybersecurity solutions rely upon detection as their core protective function. MetaDefender Deep Content Disarm and Reconstruction (Deep CDR) does not rely on detection. It assumes all files could be infected and rebuilds their content using a secure and efficient process. It supports more than 100 file types, and outputs safe and usable files. Deep CDR is extremely effective in preventing targeted attacks, ransomware, and other types of known and unknown malware threats.
Highest Threat Detection with Multiscanning
MetaDefender Multiscanning uses multiple anti-malware engines to provide highest detection rates of known threats and deliver extremely fast malware outbreak prevention. MetaDefender customers can simultaneously leverage the combined threat prevention capabilities of more than 30+ anti-malware engines using both signature/heuristic scanning and machine learning capabilities.
Detect Vulnerable Software Before Installation
All applications contain vulnerabilities of different degrees of severity that threat actors can exploit. Our File-Based Vulnerability Assessment of binaries and installers detects known vulnerabilities within files and application vulnerabilities in software programs before they are installed on endpoint devices, including IoT devices. We support vulnerability detection for over 1 million files and over 20,000 applications.
Detect Sensitive Data in Files and Emails
MetaDefender Proactive Data Loss Prevention (Proactive DLP) can help prevent potential data breaches and regulatory compliance violations by detecting and blocking sensitive data in files and emails, including credit card numbers and social security numbers. MetaDefender Proactive DLP supports a wide range of file types, including Microsoft Office and PDF.
Analyze Threat Data from Multiple Sources in Real-Time
Our Threat Intelligence Platform analyzes millions of data entries from thousands of in-the-wild devices across the world and develops a cloud-based database with billions of data points for binary reputation, vulnerable hashes, malware outbreak samples, and many other security intelligence data. Our highly reliable and scalable service-oriented system is built and maintained by our talented engineering team, offering one of fastest file hash lookup service in the market.
Detect Sensitive Data in Files and Emails MetaDefender Deploys in the Cloud or in Local Environments
Customers can implement our industry-leading Deep Content Disarm and Reconstruction, Multiscanning, and File-Base Vulnerability Assessment technology through either our MetaDefender Cloud service or by deploying MetaDefender software solutions within their own environment, including air-gapped networks.
How it works
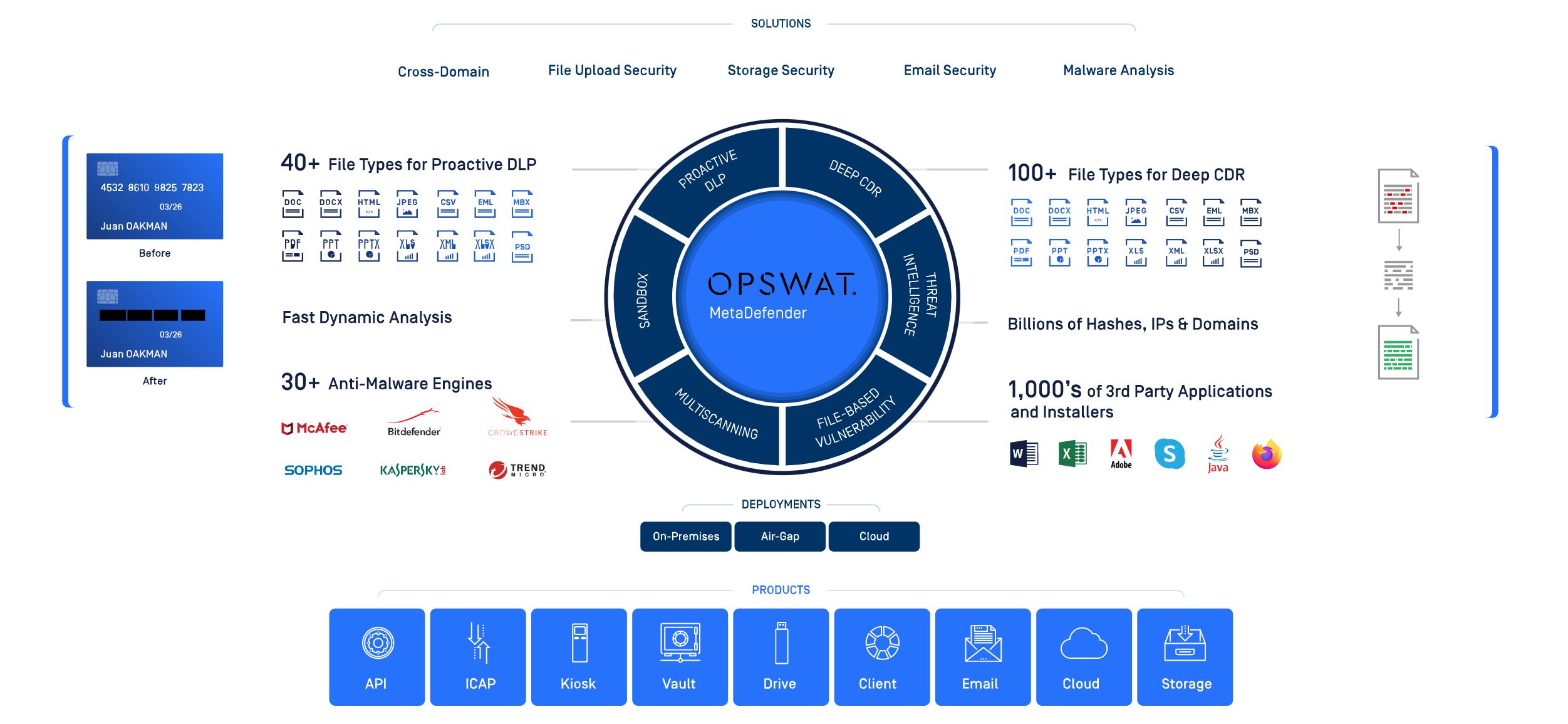
MetaDefender Technologies and Features
Deep Content Disarm and Reconstruction (Deep CDR) – Sanitize over 100 common file types, and rebuild each file ensuring maximum usability with safe content.
Multiscanning – Scan with over 30 anti-malware engines using signatures, heuristics, and machine learning technology for the highest and earliest detection of known threats.
File-Based Vulnerability Assessment – Detect known vulnerabilities in more than 20,000 software applications using over 1 billion hashes.
Proactive Data Loss Prevention (Proactive DLP) – Content-check emails and 30+ common file types for sensitive information before they are transferred.
Archive Extraction – Quickly unpack over 30 compressed file types to speed up Multiscanning and Deep CDR process and improve malware detection.
File Type Verification – Detect spoofing of over 4,500 file types and block spoofed files from entering your organization.
Custom Workflow – Customize security policies to process files in the most efficient and secure way for your organization.
Deploy MetaDefender at Major File and Data Entry Points

MetaDefender Core
For integration with existing security architectures via REST API

MetaDefender ICAP Server
For integration with web apps (via WAF, LB or API Gateway) to detect and prevent threats in file transfer process

MetaDefender Email Gateway Security
MetaDefender Email Gateway Security

MetaDefender Kiosk
For processing files entering secure networks on portable media devices

MetaDefender Core AMI
For deployment in your AWS account to process received files or protect your S3 buckets

MetaDefender Cloud
For integration in cloud and IaaS environment or with your existing SaaS products via REST API and leveraging our large hash database, IP reputation services, and more

MetaDefender Vault
For securely transferring and storing files entering networks

MetaDefender Drive
For inspecting devices before they enter facilities and networks

MetaDefender for Secure Storage
For integration with cloud storage and on-premises storage solutions
