CYBERSECURITY EDUCATION & STRATEGY DEVELOPMENT
The proposed service is providing the team with an experienced GRC professional to help with the development of cybersecurity strategy and strategic plan for security improvement.
Should there be further requirements, our consultants can also provide direction and oversight to running the information security improvement program and/or projects, while Your Business uses in-house resources to perform the security management work.
Additionally, Gadget Access’s CISO On Demand service will also enable Your Business to leverage the other services that we have on offer. Our consultants acting as outsourced CISOs have access to our full team and partner organisations, including Content Security’s team, which include other governance, risk and compliance consultants, technical security consultants, engineers and architects, penetration testers and offensive security experts, as well as security operations analysts, digital forensics, and incident response experts. These consultants can be drawn upon by the CISO consultant, or for more detailed requirements, the CISO can facilitate a direct conversation or additional engagement as required to remediate specific aspects of the CEPT security program.

SCOPE OF WORK
The Scope of Work (SOW) will be to provide “CISO on Demand” service to support the development of the ’s information security strategy, based on an initial consulting period of 3 months, commencing from the date of proposal acceptance.
Gadget Access will assign a GRC consultant to act as Cyber Security Specialist for the . The consultant will obtain detailed knowledge about the environment and be able to take specific circumstances and security requirements into account. This will allow the consultant to respond to enquiries efficiently and effectively.
The CISO on Demand will hold security management qualifications such as ISO 27001, CISSP, CRISC, CISMP, and CISM, and have at least 10 years of experience in technical and business security. If the consultant is replaced for any reason, the new consultant will have at least these qualifications. The service can also utilise Gadget Access resources, if necessary, to assist the in their security requirements. the will have access to the depth of knowledge and experience of Gadget Access without being required to employ a dedicated security team.

DELIVERABLE
Provide a tailored executive level cyber security awareness workshop to enhance security understanding at the executive level.
For the development of information security strategy, based on our understanding of the ’s requirement, the consultant for CISO on Demand will conduct interview meetings with senior management team(s) and key stakeholders of the ’s information security management, as well as reviewing existing information security management related artefacts, and relevant business strategy documentation.
The result of outlined activities will enable us to identify and document:
- Business context including business mission, goal, and objectives;
- Information security goals and objectives in alignment with the business direction; and
- Information security strategic framework and program/plan to achieve the goals and objectives.
The strategic documentation will have a high-level executive summary for communication with top management, as well as more detailed information for information security team.
ASSUMPTIONS
This proposal is based on the following assumptions. Additional charges may apply if any of these assumptions is proved invalid either prior or during the delivery of the services. Additional charges will be managed following the Project Governance section and Terms and Conditions described in Appendix C.
- All discussions will be held at the office, or where possible, remotely over audio/video conferencing considering the potential COVID-19 restrictions;
- There is no requirement for Gadget Access personnel to have any government security clearance;
- Requirements to have NSW Working With Children (WWC) clearance; and
- All information/documentation, as deemed relevant to this engagement, will be made available in a timely manner to Gadget Access consultants.
- The engagement will be commenced and completed over a predefined number of engagement hours. The use of engagement hours may be optimised with the use of video conferencing.
ENGAGEMENT METHODOLOGY
Step 1: Cybersecurity Context Establishment
Objective: “To engage with the key stakeholders of information security within the organisation and identify external and internal issues that are relevant to its purpose and that affect its ability to achieve the business goals and objectives.”
Step 2: Cybersecurity Strategic Planning
Objective: “To identify and plan for information security’s long-term goals, timelines and metrics.”
Step 3: Information Security Strategy Document
Objective: “To prepare and provide an information security strategy document that includes a long-term, coherent, and measurable strategic direction to achieve the business goals and objectives.”
CISO ON DEMAND – AVAILABLE SERVICES
1. GOVERNANCE
1.1. INFORMATION SECURITY FRAMEWORK
An information security framework helps the business manage and protect the information in a consistent and cohesive way, provide a showcase of management commitment to protect the brand from cyber threats, and improve the effectiveness and efficiency of security controls. Having a compliant framework also ensures that information security requirements are aligned with business goals and objectives, and that security is everyone’s responsibility and ownership.
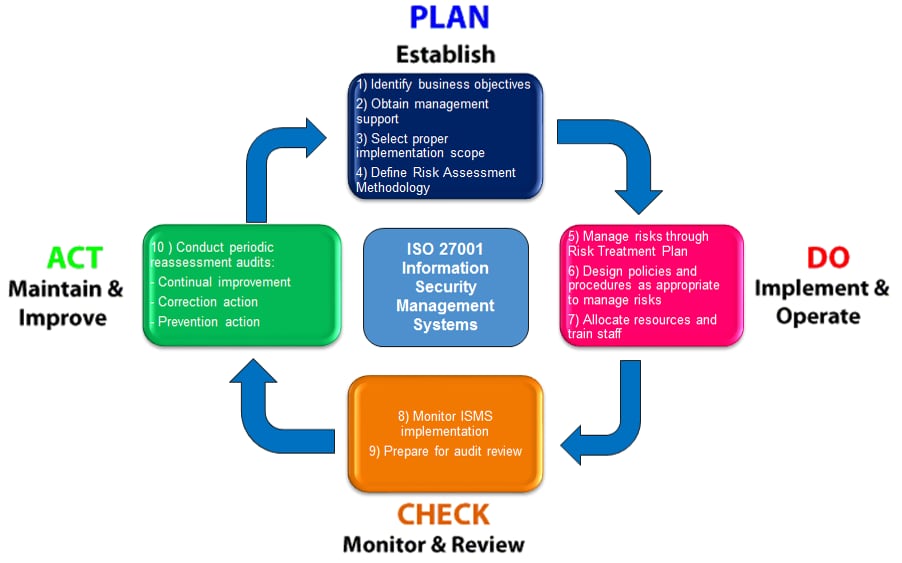
Gadget Access will follow requirements identified by ISO 27001 standard to assist in establishing and implementing an information security framework. The engagement will follow the plan-do-check-act (PDCA) model, as shown in the following:
1.2. BUSINESS CONTINUITY MANAGEMENT
The ultimate goal of Business Continuity Management (BCM) is to plan, establish, implement, operate, monitor, review, maintain and continually improve a documented management system to protect against, reduce the likelihood of occurrence, prepare for, respond to, and recover from disruptive incidents when they arise.
Gadget Access will follow the requirements identified by the ISO 22301 (Business Continuity standard) through the following roadmap:
Business Continuity Governance
Objective: “To set the strategic direction for an organisation’s Business Continuity and allow management to communicate its goals and expectations.”
Business Impact Analysis and Risk Assessment
Objective: “To establish, implement and maintain a formal and documented process for business impact analysis and risk assessment that includes:
- establishes the context of the assessment, defines criteria and evaluates the potential impact of a disruptive incident,
- takes into account legal and other requirements to which the organisation subscribes;
- includes systematic analysis, prioritization of risk treatments, and their related costs;
- defines the required output from the business impact analysis and risk assessment, and
- specifies the requirements for this information to be kept up-to-date and confidential.”
Recovery Strategy
Objective: ” To develop recovery strategies and procedures for all critical business functions derived from the business impact analysis exercise, and to establish maximum tolerable downtime (MTD) and recovery time objectives (RTO) for all critical business functions.”
Business Continuity Plan: “ To establish a formalised Business Continuity Plan that provides:
- emergency notification and disaster declaration procedures;
- recovery team procedures;
- facilities and business restoration procedures;
- BCP testing and maintenance cycles;
- Appendices for master contact list, equipment inventories, connectivity schematics, etc.
- Providing workshop to Your Business management and key business owners ensuring they understand the Business Continuity Plan.“
1.3. CISO ON DEMAND
Chief Information Security Officer (CISO) is a C-level manager that is responsible for developing and communicating information security strategy for the entire business and advising the business on successful deployment of the strategy within the environment.
To achieve this and as part of the CISO as a Service, Gadget Access will be engaged with the business on an ongoing basis that will fulfil the above requirements including:
- Security strategy and architecture
- Compliance advisory services;
- Any ongoing security concerns or issues;
- Security events that have occurred in the client environment;
- Security requirements for new internal projects;
- New trends in the security industry;
- Updates on remediation progress.
1.4. GAP ANALYSIS
Your organisation needs to know how well it is protecting your data and business processes and keeping the trust of your customers and clients. A gap analysis will analyse your current security posture and compare it with cyber security standards such as ISO 27001 and NIST Cybersecurity Framework to see where your organisation stands and how it compares with the industry and your competitors. The result of this assessment will help the organisation to define a strategical, risk-driven roadmap to improve the effectiveness and efficiency of security controls up to a recommended level within their industry.
The gap analysis will:
- Identify information security goals and desired controls’ maturity level;
- Determine the maturity and effectiveness of current security controls;
- Provide a meaningful executive summary that will help your executive and board understand the organisation’s part of the security journey; and
- Provide an information security roadmap and strategy for moving forward
1.5. INFORMATION SECURITY AUDIT
Gadget Access can perform tailored information security audits that determine whether your organisation’s current procedures, controls, processes, arrangements and other activities within the Information Security Management System (ISMS) are in line with information security standards, applicable regulations, and the organisation’s policies. The audit will allow you to determine whether your ISMS is effectively and efficiently implemented and maintained.
Our audits will allow you to check the effectiveness of your controls and fit into the Plan Do Check Act framework for an ISMS.
Regular audits at planned intervals are required to identify whether the information security controls:
- Meet the organisation’s context and risks pertaining to information security.
- Are effectively implemented and maintained.
- Are defined using a risk-based approach and there is an existent and updated set of policies and standards that have been defined, approved by management, published and communicated to employees and relevant external parties.
2. TECHNICAL AUDIT
2.1. PENETRATION TESTING
In the same way car manufacturers test the safety of cars through crash testing, organisations test the security of their IT systems by testing their resilience against an active attack. Penetration testing simulates such an attack, using the same tools and techniques used by criminals, malicious insiders, and other attackers.
An experienced security consultant will use a combination of manual and automated techniques to identify vulnerabilities. Once vulnerabilities have been identified, the tester will attempt to exploit them, seeing what additional access, information, and privileges are gained.
We can perform penetration testing on:
- External environment
- Internal environment
- Wireless networks
- Web/Mobile Applications
The outcome will be a report containing the security issues that affect your project, as well as recommendations on how best to fix or mitigate these issues. The tester will also be available for a debrief to ensure that the vulnerabilities are understood and can be resolved.
2.2. PENETRATION TEST RESPONSE
A penetration test is not just a chance to see the vulnerabilities in your system, but a way to see the impact that would occur if the vulnerability is exploited. To determine the full impact that a real hack would have, it is important to see how well your organisation would be able to respond to the hack, and whether your organisation has the response capability to properly determine what happened.
Gadget Access’s Penetration Test Response service brings in a member of our Incident Response team to treat the penetration test like a real hack. The responder will work with your internal security systems and logs to find out:
- If you were hacked with these vulnerabilities, would you be alerted?
- If so, would you be able to stop it?
- If not, would you have the security systems, logging, and incident response capability to effectively respond?
The responder will work in partnership with the tester to provide an effective and real-world analysis of your response capability. The responder will analyse the detection and response capability of each high-risk vulnerability as well as the general response capability.
To get the full benefit, the responder will require access to your logs and security systems and may potentially choose to analyse forensic images of systems in your organisation.
The expected benefits of this service are:
- Provide visibility over the effectiveness of your incident response in your organisation.
- Provide real-world information over what would happen if you were targeted by a real hacker.
The deliverable of this service will be:
- An analysis of the response capability of your organisation, based on the detection and response capability on the actions taken by the penetration tester.
- A high-level session on the results of the Penetration Test Response delivered as part of the penetration test debrief. This service is provided by a member of the incident response team. In rare occasions, if there is a high priority incident that occurs with another client the responder may need to pause the delivery and attend to the other client.
This service is provided by a member of the incident response team. In rare occasions, if there is a high priority incident that occurs with another client the responder may need to pause the delivery and attend to the other client.
2.3. SOE AUDIT
Weak configurations can expose systems to unnecessary risk. Configuration reviews ensure that the systems are appropriately hardened, with security features enabled and working effectively.
Gadget Access can perform configuration reviews against security best-practices, compliance standards and benchmarks, internal organisation standards, and known attack vectors with special consideration to the purpose of the operating environment.
2.4. ACTIVE DIRECTORY AUDIT
Weak Active Directory settings can put the entire organisation at risk. Weak domain server settings can lead to the compromise of domain administrator accounts. Weak group policy can lead to compromises of user devises.
Gadget Access can perform an audit of the Active Directory domain for security vulnerabilities and misconfigurations. The audit will uncover both exploitable conditions and opportunities to further improve security.
2.5. VULNERABILITY ASSESSMENT
Vulnerability assessments are effective at maintaining visibility over security issues in the environment between penetration tests. By performing regular vulnerability assessments, issues that arise during the year can be identified and closed.
A Security Assurance consultant will use Tenable Nessus Professional to scan the network for common vulnerabilities, default credentials, missing patches, and security misconfigurations.
2.6. FIREWALL REVIEW
Firewalls are the key gateway to your internal network. It is critical that they appropriately control traffic, letting only necessary traffic in and out.
A firewall review will ensure that the firewall ruleset includes only the necessary rules, with all traffic that should not be there, being blocked.
2.7. ACCOUNT AUDIT
Even with account management practices in place, accounts of terminated employees and leftover administration accounts can still be left in systems. Account audits are effective at picking these accounts up before they are used to target the organisation.
Gadget Access will perform account audits on the following systems:
- Active Directory
- Linux
- Applications
2.8. PASSWORD CRACKING
User accounts with weak passwords are a common method of compromising internal accounts. When performing password cracking, Gadget Access will use the same tools and techniques that attackers would use to attempt to obtain the original passwords. The accounts that are compromised can then have their passwords reset and secured.
Gadget Access will perform password cracking on the following systems:
- Active Directory
- Linux servers
2.9. RED TEAM ENGAGEMENT
A red team engagement plays out a specific security scenario where the Red Team are the attacking team (in this case, malicious hackers) and the Blue Team are the defending team (in this case, the incident responders). The aim of the engagement is to test all levels of security controls within the organisation while simultaneously testing the incident response plan in a predetermined attack scenario.
Gadget Access will develop a scenario that will simulate the attacks a competent team of hackers would attempt during an attack specifically targeting Your Business as an organisation. The engagement is highly technical and highly targeted, forming a complete test of the resilience against advanced threats.
2.10. SUPPLIER AUDIT
With increased regulatory scrutiny, continuing cost pressures, active investors, and a vigilant public, businesses today must have a clear understanding of the risks that are inherent in external business relationships. By recognising and proactively addressing these third-party issues, business leaders can reduce exposure to risk and achieve stronger relationships with service providers, suppliers, and delivery partners.
Gadget Access’s Third-Party Assessment Framework will enable the business to gain an understanding of the controls implemented by their Suppliers, assess the maturity of those controls and make a well-informed decision on the viability of the Supplier based on the business requirements.
3. PROFESSIONAL SERVICES/SOLUTION SUPPORT
Security systems and products require tuning, configuration, support and maintenance for the latest attack vectors and trends. Without support, the systems will provide little to no protection capabilities for Your Business.
Gadget Access can provide the security engineering solution support you need to make sure your security is effective.
4. MANAGED SERVICES
Gadget Access can provide a completely managed service for the systems we support. We will perform the maintenance and updates, and manage all changes to the solution. You can be certain your security objective will be achieved.
ABOUT GADGET ACCESS
A TRUSTED POINT-OF-CONTACT FOR ALL YOUR CYBER SECURITY REQUIREMENTS

WHO WE ARE
Gadget Access is an Australian IT security integration and consultancy firm with offices in Sydney. Founded in March 1995, we focus on protecting our customers’ brands, reputations and bottom-lines from the evolving threat and regulatory landscapes. We do so by partnering with key technology vendors and providing practical expertise on good governance, security architecture, secure cloud, advanced forensics and more.
OUR MISSION
Our vision is a more cybersafe Australia, and therefore our mission is to empower businesses in cyber security. This means providing a single touchpoint for cyber security solutions, services and knowledge. Our industry expertise means that we not only design and implement a comprehensive range of security solutions, but offer these as fully integrated, managed services for our customers.
WHY CHOOSE US?
INDUSTRY EXPERIENCE
We are a wholly Australian-owned information security advisory organisation with over 20 years of specialist experience in both the public and private sectors. We provide information security services and solutions to more than 1000 clients Australia-wide, across education, mining, government, health, finance, utilities, not-for-profit, retail and more. We understand the unique information security challenges facing each sector and deliver industry-specific answers to ensure your enterprise has a relevant and effective information security posture.
COMPREHENSIVE PARTNER
Gadget Access is one of the only organisations in Australia covering the information security space end-to-end. We specialise in security program management and have partnered with leading security organisations to offer a complete end-to-end service across Penetration Testing, Governance, Risk & Compliance, Managed Services, Digital Forensics & Incident Response, Security Awareness Training and more.
INNOVATION
Drawing on a wealth of industry experience, Gadget Access have developed a number of innovative services in the cyber security market. Today, we offer the following innovative services to our clients:
- On Demand Penetration Testing: This provides frequent penetration tests to our clients for a very reasonable cost. This is in addition to the manual penetration tests we offer.
- Active Defence: A proactive service identifying actual breaches & suspicious activity on your network that haven’t been picked up by existing security controls.
- Third-Party Risk Assessments: We have developed a service around our specialised platform where we conduct large scale risk assessments of all your suppliers within hours, giving you full visibility of the risk they pose to your business.
- Managed Cybersecurity Awareness Program (MCAP): This is a fully managed service revolving around easy and more effective security awareness training. MCAP fills the gaps for small businesses that lack the bandwidth to run their own programs and for larger enterprises that a need more frequent, formalised style of training.
WORKING WITH THE BEST OF THE BREED
There’s no one-size-fits-all in cyber security. That’s why we always scour the full marketplace and tailor strategic solutions to each client’s needs. As a trusted partner to many, we have the responsibility to provide well-informed, consultative services backed by unbiased market and brand research. We partner with the top technology vendors, some of which include:

CLIENT SERVICES TEAM
We understand that providing outstanding service to our clients goes beyond our expertise, technical services and solutions. Excellence begins with putting the needs of our clientele first, and that’s why we’re committed to providing quality communications and assistance at every step of the way. This year, we created our Client Services Team as a means of doing so. Their purpose is to uphold consistent engagement with clients and offer accessible support at every level of interaction.
PANELS
Our financial stability, probity and pricing has enabled us to become an approved supplier for a number of panels, including but not limited to:
- Australian Government Digital Marketplace.
- NSW Government Contract No. 2360 (Telecommunications) and No. 2020 (Information Technology).
- Local Government Procurement Contract No: 10.08 IT&C (Professional Services).
- eServices Register (Victorian Government).
- QLD Government GITC Q-5055.
- Chamber of Commerce and Industry Queensland QAssure Accredited Business.
CERTIFICATIONS
We proudly validate our stance as a leading security advisory firm by continually learning and gaining the necessary credentials to keep our clients, our partners and ourselves secure:
- ISO 27001 Lead Auditor and Implementor.
TERMS AND CONDITIONS
Gadget Access Pty Limited (“Gadget Access”) agrees to provide the services specified in the Proposal and the Client agrees to pay the fees specified in the Proposal in relation to these services.
CONFIDENTIALITY AND INTELLECTUAL PROPERTY
Each party shall keep all information obtained in connection with the services (“Confidential Information”) confidential and must obtain the express consent of the other party before disclosing any information to any third party.
All intellectual property, including copyright, developed by Gadget Access in the course of the service (“Intellectual Property”) vests in Gadget Access. Gadget Access grants a non-exclusive perpetual license to the Client to use the Intellectual Property.
Nothing shall prevent Gadget Access from providing the Confidential information to any of its advisors, legal representatives or where required by law.
INDEMNITY
The Client indemnifies Gadget Access against prosecution, claims, liability or loss including any costs, charges or expenses arising from its proper performance of the services.
LIABILITY
Gadget Access is not liable for any loss, damage, expense or cost incurred by the Client arising out of:
- Compliance with any instruction or direction from the Client;
- Provision of any Action or Deliverable based on the Client Information;
- Delay, non-receipt or receipt of any Client Information;
- Proper performance of the Security Audit.
Gadget Access’s liability under the Proposal and these Terms and Conditions is limited to the sum of Fees paid by the Client under the Proposal.
NON-SOLICITATION
During the term of this Agreement and for a period of 2 years after any termination of this Agreement, the Customer will not, without the prior written consent of Gadget Access Pty Ltd, either directly or indirectly, on the Customer’s own behalf or in the service or on behalf of others, solicit or attempt to solicit, divert or hire away any person employed by Gadget Access Pty Ltd or any customer of Gadget Access Pty Ltd.

