A Quick Look at ISA/IEC 62443
Hello, cybersecurity enthusiasts! If you’re in the industrial automation and control systems (IACS) space, or even if you’re just a cybersecurity professional looking to broaden your knowledge, you’ve probably heard of the ISA/IEC 62443 standards. Today, we’re diving deep into this topic to give you an exhaustive understanding of what these standards are, why they matter, and how to navigate their complexities.
Introduction to ISA/IEC 62443
The ISA/IEC 62443 set of cybersecurity standards is a big deal. Created by the International Society of Automation (ISA) and co-developed by Europe’s International Electro-technical Commission (IEC), these standards have gained global recognition. They were even endorsed by the United Nations for their Cybersecurity Common Regulatory Framework in 2019. In 2020, a new part (3-2) was added to provide guidance on performing risk assessments on IACS.
In 2021, the standard became a horizontal standard, meaning it will serve as the foundation for all future ISA and IEC industry-specific industrial security standards. This is a significant move, considering most ICS security standards are usually tied to a specific industry, nation, or government body.
The Essentials: What You Need to Know
If you’re an asset owner or responsible for protecting an industrial site, the following sections are your go-to:
- 1-1: Terminology, concepts, and models
- 2-1: Security program requirements for IACS asset owners
- 3-2: Risk assessments for system design
- 3-3: Security requirements and security levels
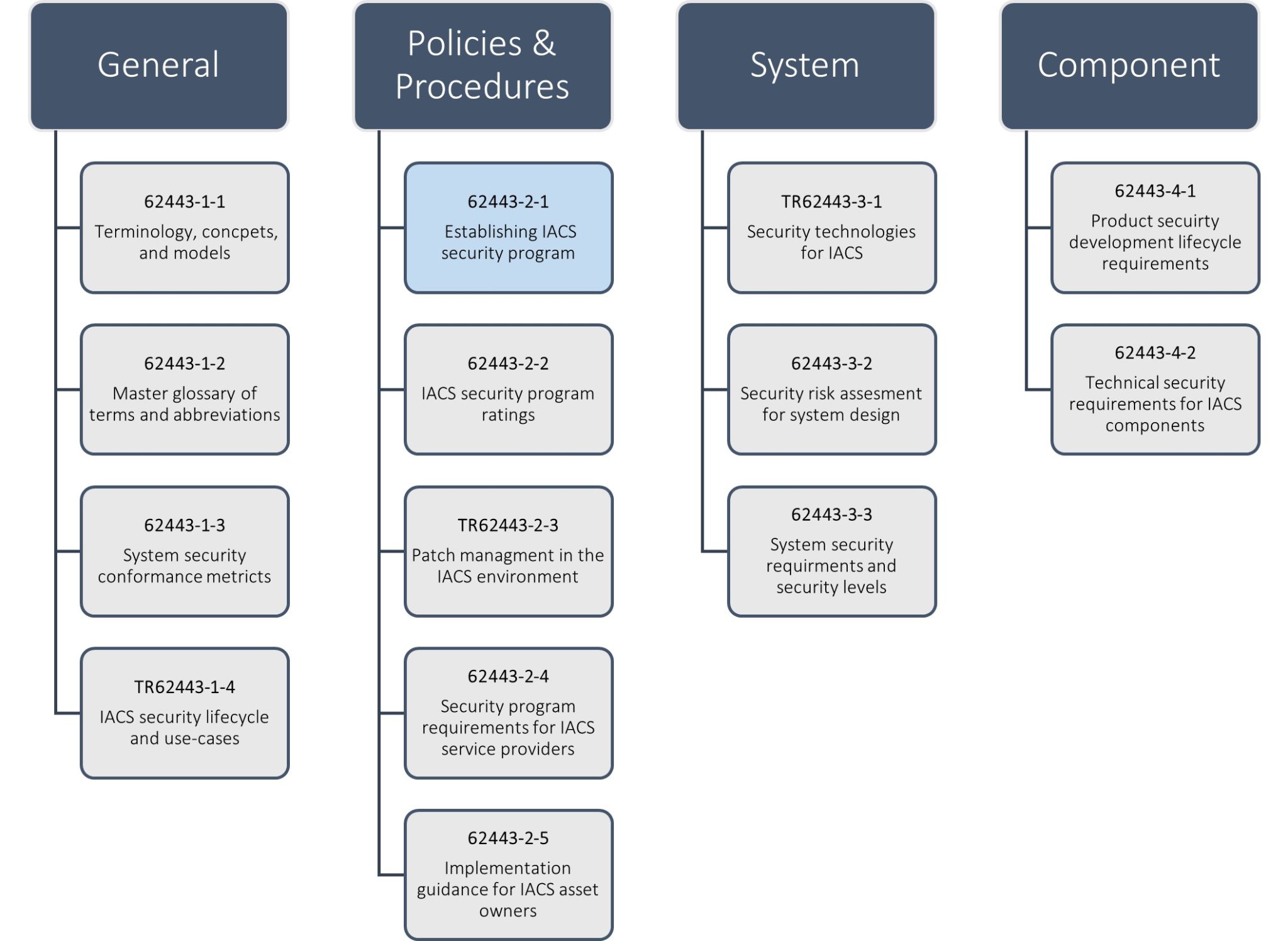
Figure 1: ISA/IEC 62443 Standards most relevant to industrial asset owners & operators
How to Access the Standards
Getting your hands on these standards isn’t free, but the ISA offers a free Quick Start Guide that’s worth downloading. If you’re serious about this, consider becoming an ISA member. The membership fee is less than the cost of purchasing two or three volumes of the standards, and you get free access to ISA and IEC 62443 standards.
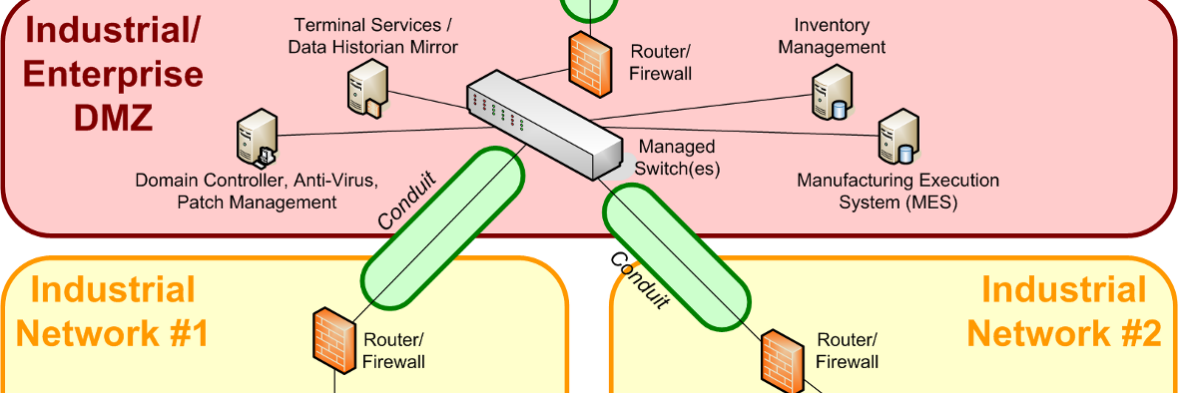
Implementing the Standard
Implementing ISA/IEC 62443 involves setting up a security program as described in section 2-1. You’ll need to perform a risk assessment based on section 3-2 and make necessary changes to your network and security design. Your site’s cyber defenses will be categorized into one of five security levels, as described in section 3-3. These levels range from SL-0, which requires no special protection, to SL-4, which demands sophisticated means with extensive resources and high motivation for protection.
The Challenge: Picking the Right Security Levels
Choosing the right security level can be confusing. The current version of the standard describes security levels in terms of the characteristics of the perceived adversary, rather than the worst-case consequences of a compromise. This can lead to the wrong security level being selected.
Real-world Examples: Distillery vs. Power Plant
Let’s consider a small-batch gin distillery and a 600 MW natural gas-fed power plant. The distillery is more concerned about local competition and ransomware groups, while the power plant has to consider the potential for widespread outages and public safety risks. The nature of the consequences, not the expected adversary, should determine the security level.
Looking Ahead: Future of IEC 62443
The ISA is aware of the challenges and is working on revisions. New technologies like containerization, virtualization, edge devices, and the cloud are also being considered for incorporation into the standard.
Conclusion
ISA/IEC 62443 is a robust framework for securing industrial systems. While it has its complexities and challenges, it’s a valuable resource for anyone in the cybersecurity field. The standard is continually evolving to meet the needs of a rapidly changing landscape, making it as relevant today as it will be in the future.
So, if you’re tasked with implementing IEC 62443, arm yourself with the right knowledge and resources. It’s not just about understanding the standard but about applying it effectively to secure your assets and operations.