TA505, a well-resourced organized cybercrime ring, is known for ongoing malware authoring and development, with everything from fully-fledged backdoors to what seems like beta-stage code making appearances in its campaigns.
A new backdoor named ServHelper, developed by TA505, has been found, acting as both a remote desktop agent as well as a downloader.
The primary motive is, as usual, financial: “TA505 appears to be actively targeting banks, retail businesses, and restaurants as they distribute these malware families,” said Proofpoint researchers, and added that the remote desktop version, a.k.a. the “tunnel” variant, was seen in November 2018 spreading via a few thousand spam messages that contained Microsoft Word or Publisher attachments with macros that, when enabled, download and execute the malware. This version focuses on setting up reverse SSH tunnels to allow the threat actor to access the infected host via Remote Desktop Protocol (RDP).
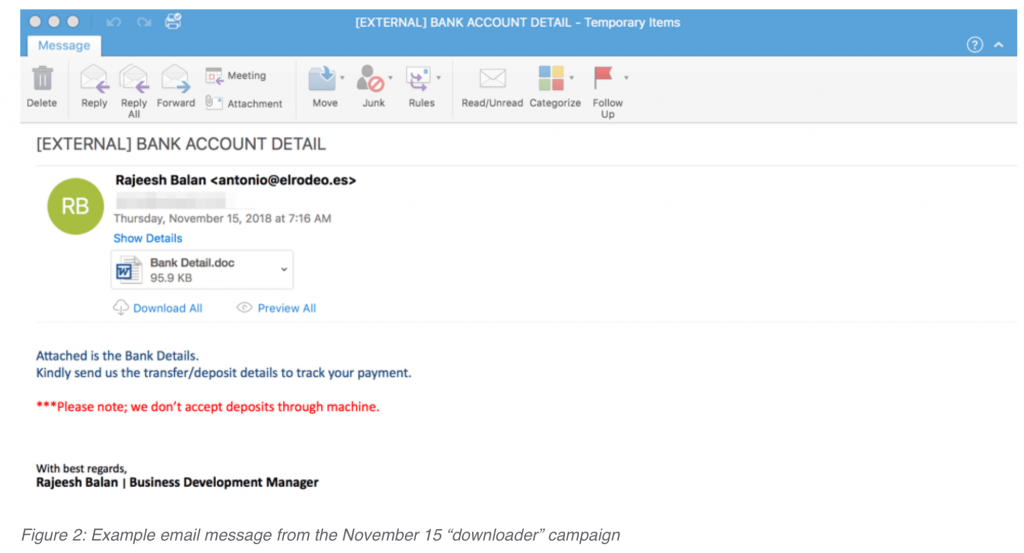
In December 2018, TA505 mixed it up with another downloader variant campaign. It targeted retail and financial services customers again, but this time used a mixture of Microsoft Word attachments with embedded malicious macros; PDF attachments with URLs linking to a fake “Adobe PDF Plugin” webpage (which linked to the malware); and direct URLs in the email body linking to a ServHelper executable.